Leaks Are Messages, Not Accidents
Leaks are usually described as failures.
A system failed. A protocol was bypassed. Someone made a mistake.
In the public imagination, a leak is treated as an anomaly — an unfortunate exception in an otherwise functioning structure. Something that should not have happened, but did. Something to be fixed, patched, or prevented next time.
That interpretation is comforting. It suggests that once the technical flaw is corrected, the problem disappears.
Counterintelligence looks at leaks very differently.
From that perspective, leaks are rarely accidents. They are signals. And signals exist to be read.
A leak is not just information escaping containment. It is information moving at a specific moment, through a specific channel, toward a specific audience. When you look at leaks that way, the question changes. It is no longer “what went wrong?” but “what message is being sent — and to whom?”
Most public debates never reach that level. They focus on morality, legality, or ideology. Important discussions, perhaps — but analytically incomplete. Because they miss the strategic function of the leak itself.
That is the gap this episode explores.
My name is Alexandre Andrade. I’m a counterintelligence analyst. And today, I want to examine one of the most famous leaks of the last decades — not as a moral controversy, but as a strategic message.
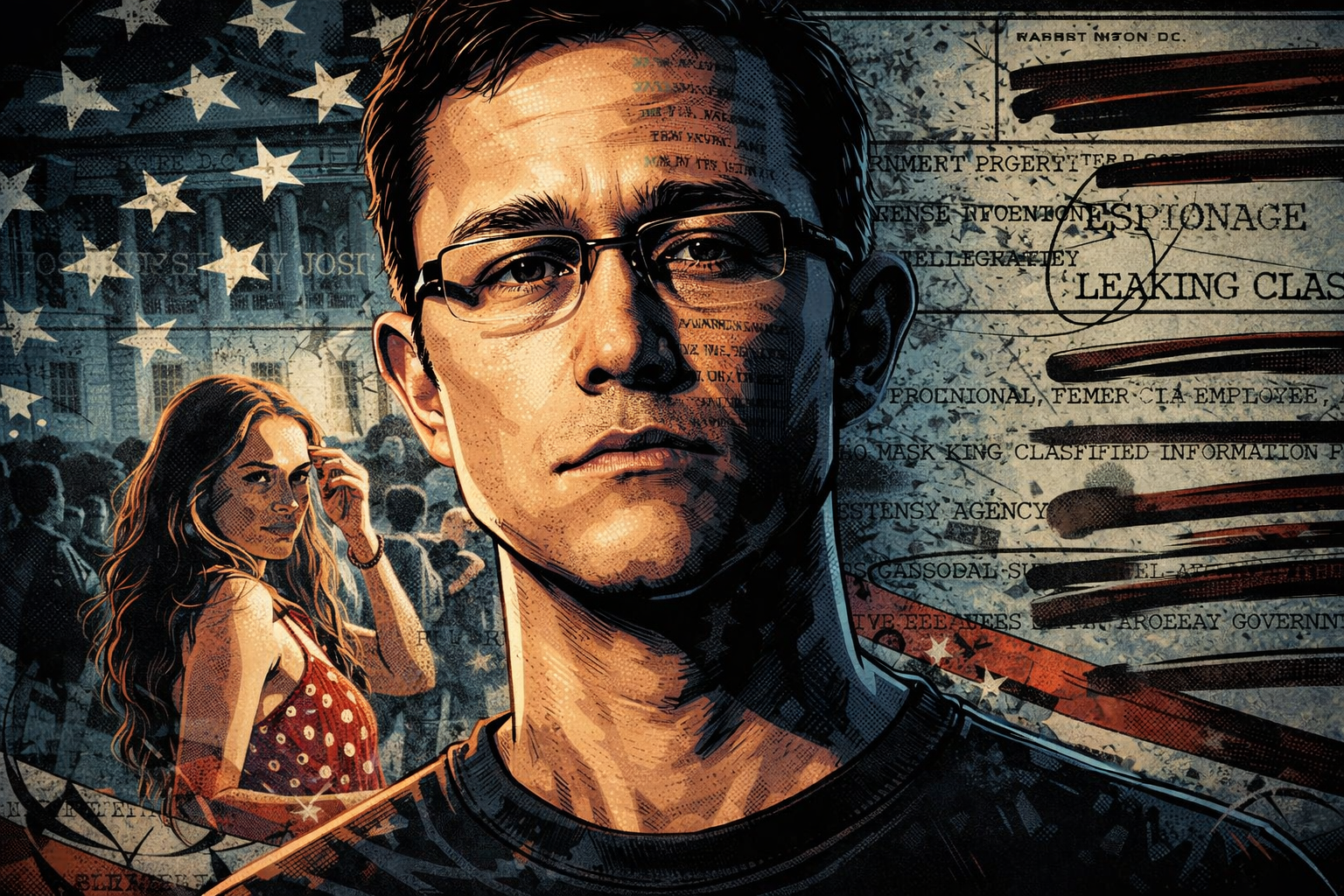
In 2013, Edward Snowden disclosed a vast collection of classified documents related to U.S. and allied surveillance programs. The scale was unprecedented. The impact was global. Governments reacted, companies adjusted, and public trust shifted in lasting ways.
The public debate quickly collapsed into a binary frame: hero or traitor. Whistleblower or criminal. Defender of privacy or threat to national security.
That framing dominated headlines and still shapes how the case is remembered.
From a counterintelligence perspective, however, that debate is secondary. Because regardless of how one judges Snowden’s intentions, the event itself followed a pattern that professionals recognize immediately.
This was not a chaotic data spill. It was a curated release. Information was selected, staged, timed, and amplified through trusted intermediaries. The leak did not simply expose facts. It reshaped the information environment.
To understand why that matters, we need to step away from the individual and examine the structure.
Let’s start with the human layer.
Every major leak begins with access. And access always comes through people. Not hackers breaking in from the outside, but insiders already trusted by the system.
From a counterintelligence standpoint, Snowden was not an anomaly. He fit a well-known profile: technically skilled, granted broad access, operating in a compartmentalized environment, and increasingly isolated from the institutional culture around him.
Isolation is not always physical. Often, it is cognitive and moral. The individual begins to feel disconnected from decision-makers, convinced that they alone see the truth clearly. That sense of moral clarity is powerful — and dangerous.
At that point, rationalization begins. The insider reframes their role. They are no longer violating trust; they are correcting injustice. They are no longer breaking rules; they are serving a higher purpose.
This is not unique to intelligence services. The same dynamic appears in corporations, law firms, financial institutions, and family businesses. Access plus grievance plus moral justification is a recurring formula.
One of the most consistent errors insiders make is overestimating their control over consequences. They believe they can decide what the information will do once released. In reality, once information leaves containment, control shifts immediately to others.
That brings us to the second layer: information itself.
The Snowden disclosures were not released in bulk. They were curated. Documents were selected, contextualized, and handed to specific journalists and media organizations. The release was gradual, not instantaneous.
From a counterintelligence perspective, that is not incidental. That is staging.
Gradual release creates sustained pressure. Each new disclosure reactivates the story, extends its lifespan, and forces repeated institutional responses. It also prevents effective containment, because organizations are always reacting to the last revelation, never the full picture.
Equally important is the choice of intermediaries. Journalists with credibility, global reach, and moral authority were not just messengers; they were force multipliers. Their legitimacy transferred to the information itself.
This is a critical point. The power of a leak is rarely in the data alone. It lies in who carries it, how it is framed, and how audiences are guided to interpret it.
Information, in this sense, is not merely released. It is performed.
Once you see that, the idea of leaks as accidents becomes difficult to sustain.
Now consider the institutional layer.
One of the most striking aspects of the Snowden case was the initial response — or lack of it. Fragmented messaging, delayed reactions, and an apparent absence of a coherent narrative allowed external actors to define the meaning of the disclosures.
From a counterintelligence standpoint, silence is not neutral. Silence is interpreted. And in information environments, early interpretation tends to become dominant interpretation.
Institutions often believe that restraint signals responsibility. Sometimes it does. But in the context of a leak, delayed response frequently signals confusion, internal disagreement, or unreadiness — all of which amplify the leak’s impact.
Another common mistake is over-focusing on the individual. Pursuing the leaker becomes a substitute for examining systemic vulnerabilities. The organization treats the event as a betrayal, not as a signal of deeper failure.
This is analytically comforting but strategically flawed. Because individuals exploit weaknesses that already exist. They do not create them.
At this point, it is important to address the obvious counterarguments.
Many will say: Snowden exposed wrongdoing. Others will argue that the public had a right to know. Some will insist that without such leaks, accountability is impossible.
From a moral or political standpoint, those arguments deserve discussion. From a counterintelligence standpoint, they are largely irrelevant.
Intent does not neutralize impact. Good motives do not prevent strategic consequences. Systems are not evaluated by virtue, but by effect.
A leak can simultaneously reveal genuine problems and create new vulnerabilities. Both can be true at the same time.
This is where public discourse often fails. It treats moral judgment as analysis. Counterintelligence treats analysis as separate from judgment.
When we step back from the Snowden case, a broader pattern becomes visible.
Leaks function as instruments of internal conflict. They surface when internal trust collapses, when grievance outweighs loyalty, and when institutional feedback mechanisms fail.
They rely on asymmetry. The leaker prepares quietly; the institution reacts publicly. The leaker controls timing; the institution absorbs impact. The leaker speaks once; the institution must respond indefinitely.
Most importantly, leaks reveal that information environments are contested spaces. They are not neutral channels. They are arenas where power is exercised through exposure, framing, and silence.
This pattern does not belong to intelligence agencies alone.
If an organization with immense resources, legal authority, and security culture can be destabilized this way, consider what that implies for the private world.
Corporations, boards, law firms, investment funds, and family enterprises operate with far fewer protections. Access is broader. Loyalty is assumed. Grievances are often ignored until they become visible.
In those environments, leaks rarely look dramatic. They appear as quiet disclosures, selective conversations, documents shared at the right moment with the right people. By the time leadership realizes what happened, the narrative is already set.
The lesson is not paranoia. It is attention.
Leaks are not random failures. They are messages. And like all messages, they reveal more about the system than about the messenger.
The question is not whether leaks can be prevented entirely. They cannot. The question is whether organizations are capable of reading the signals before the message is delivered publicly.
Most are not.
And that, more than any individual act, is the real vulnerability.